There are a number of ways in which cyber attacks can occur, this meaning an offensive action that targets computer information systems, infrastructures, computer networks or personal computer devices, using various methods to steal, alter or destroy data or information systems.

Here are 10 variations of cyber attack and what exactly they are and how they work.
1 . Password Attack
Passwords are the most commonly used method of information systems to authenticate users, meaning obtaining them is an extremely common and effective approach an attacker will take. There are a few ways in which passwords can be obtained including brute-force and a dictionary attack.
Brute-force is password guessing using a random approach, trying a number of different passwords hoping that one will work. Trying passwords related to the persons name, hobbies, job or other personal information is commonly used here.
A dictionary attack is where a dictionary of common passwords is used in order to try and access information on another person’s device or network.
2 . Man-in-the-Middle (MitM) Attack
A man-in-the-middle (MitM) attack involves a hacker intercepting the communications between an unaware victim and the entity in which they are trying to communicate. For example, you may think you are entering your banking details on the bank’s legitimate website, however the man-in-the-middle has created a look-alike site and now has access to your online banking details.
Such attacks can occur in two ways, with the man-in-the-middle being close to the victim in terms of proximity, often in public areas with free WiFi hotspots, or with malicious software (malware). There are a number of types of man-in-the-middle attack, including IP spoofing, HTTPS spoofing, email hijacking, WiFi eavesdropping and DNS spoofing.

3 . Phishing Attack
Phishing uses deceptive emails and websites to gain personal information from unsuspecting victims. The goal of a phishing attack is to trick the victim into believing an email they have received requires them to take action and is something that they want or need to do, ultimately leading them to follow a link or download an attachment. The hackers masquerade as legitimate and trusted organisations, often that the victim will already know and do business with. If the victim follows the link and enters any personal information, the hacker then has these details for themselves.
4 . Drive-by Attack
A drive-by attack is a common method that cyber criminals use in order to spread malware. The hacker will look for insecure websites and will then plant malicious script into HTTP or PHP code on those pages, either installing malicious software directly onto the computer of anyone who visits the site, or directing them to another site controlled by the hackers themselves. Unfortunately, these types of attacks can be hard to spot as the victim is not required to do anything to actively enable the attack, which can happen on any apps, web browsers or operating systems that have security flaws.
5 . Malware Attack
A malware attack is hackers install malicious software on a victims device without them knowing in order to gain access to personal information or to damage the device. The usual aim of this type of attack is financial gain.
 6 . Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Attacks
6 . Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Attacks
A denial-of-service (DoS) attack overwhelms a system’s resources making it unable to respond to service requests. A distributed denial-of-service (DDoS) attack is similar in that is also attacks a system’s resources, however is launched from a large number of host machines which are infected with malware and controlled by the hacker.
One purpose of these attacks can be to take a system offline to that it can then be subject to a different kind of attack, but sometimes denial-of-service attacks only provide the hacker with the satisfaction of service denial and can have no real benefit to the attacker like other forms of cyber attack do.
7 . Birthday Attack
A birthday attack exploits the mathematics behind the birthday problem in probability theory and is used to abuse the communication between two or more parties. This is a cryptographic attack considering the theory that some paired people in a set of randomly chosen individuals will have the same birthday.
8 . Eavesdropping Attack
Eavesdropping attacks can also be known as ‘sniffing’ or ‘snooping’ and involve taking advantage of unsecured network communications in order to steal information being sent or received by its user on a computer, smartphone or other connected device. Hackers usually use this kind of attack to gain sensitive financial and business information that they can then sell for criminal purposes.
9 . SQL Injection Attack
SQL injection attacks make it possible for hackers to access personal information or data that belong to other users or to an application itself, allowing them, in many cases, to modify or delete the data to cause persistent changes to the content or behaviour of the application. This type of attack allows the criminal to interfere with the queries that an application makes to its database.
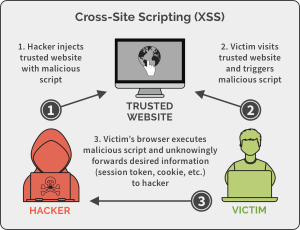
10 . Cross-Site Scripting (XSS) Attack
Cross-site scripting (XXS) attacks are client-side code injection attacks where a hacker aims to place malicious scripts in a web browser of an unsuspecting victim by including malicious code on a legitimate website or app. The attack occurs when the victim visits this website or app, which then becomes a vehicle to deliver malicious script to their browser. Message boards, forums and web pages which allow comments are the most commonly used pages for XXS attacks.
We encourage everyone to be vigilant online! Use strong passwords, install anti-virus software, manage social media settings for privacy and strengthen your home internet connection. It is also advised to learn about what is best to do if you think you have been victim of a cyber attack.
WiFi Securities’ mission is to protect businesses and the public from cyber-criminal activity. Contact us today for more information on how our SpriteGuard™ device can protect you and your customers.
enquiries@wifi-securities.com
+44 (0)151 230 2161
Twitter: @wifisecurities
Facebook: @wifisecurities
LinkedIn: WiFi Securities


 Phishing – What It Is & How To Spot It
Phishing – What It Is & How To Spot It